Configure IdP-Initiated SSO for Microsoft Azure AD (Entra ID)
Note
If your organization is using the Portfolio Financials and Capital Planning products in Procore, you will need to reach out to your Procore point of contact or the Support team to set up your Azure AD SSO.
You will need to provide the following information when requesting the setup: Single Sign On Issuer URL, Single Sign On Target URL (Optional for IdP-Initiated SSO), and Single Sign On x509 Certificate.
Objective
To configure Procore's IdP-Initiated Single Sign-On (SSO) solution for Microsoft Azure Active Directory (Azure AD).
Background
If your company manages your users with Azure AD, you can leverage its SSO capabilities. This gives your end users the ability to authenticate their identify for the Procore application using their Azure AD account. With this SSO integration, you can:
- Leverage Azure, AD for SSO access to Procore.
- Simplify your entire organization's password management process.
- Avoid problematic user password management.
Things to Consider
- Authentication Protocol:
- You can integrate the Procore application with Azure AD using the Security Assertion Markup Language (SAML 2.0).
- Requirements:
- Azure AD
- Required Permissions:
- Global Administrator rights to Azure AD.
- 'Admin' level permissions to Procore's Company level Admin tool.
Steps
- Step 1: Add Procore as a New Enterprise Application in Azure Active Directory
- Step 2: Configure the Procore Enterprise Application's SSO Settings
- Step 3: Assign Users and Groups to the Procore Enterprise Application
- Step 4: Add the Azure AD Settings to Procore
Step 1: Add Procore as a New Enterprise Application in Azure Active Directory
Step 2: Configure the Procore Enterprise Application's SSO Settings
Step 3: Assign Users and Groups to the Procore Enterprise Application
Note: This step is only required if the 'User Assignment Required' setting is enabled in the Procore Enterprise Application under Manage > Properties. This setting is disabled by default in the Procore application.
- In the Overview page for your new enterprise application, under Manage, click Users and Groups.
- Click Add User.
- Select the users to whom you will grant access to Procore.
The users names appear under the Selected Members list. - Click Select at the bottom right of the page.
Note: If you want to test the Azure Active Directory SSO integration before deploying it to your end users, add only your user account. Then, after completing the configuration steps and testing the integration, come back and assign the rest of your company's users to Procore.
The system displays a message to confirm that you want to grant access to these users. - Click Yes to confirm that you want to grant the selected users access.
A Yes will appear for each user in the 'Access' column.
Step 4: Add the Azure AD Settings to Procore
- Log into the Procore application.
Important: You must log into Procore with an account that has been granted 'Admin' level permissions to the Company level Admin tool. - Navigate to the company's Admin tool.
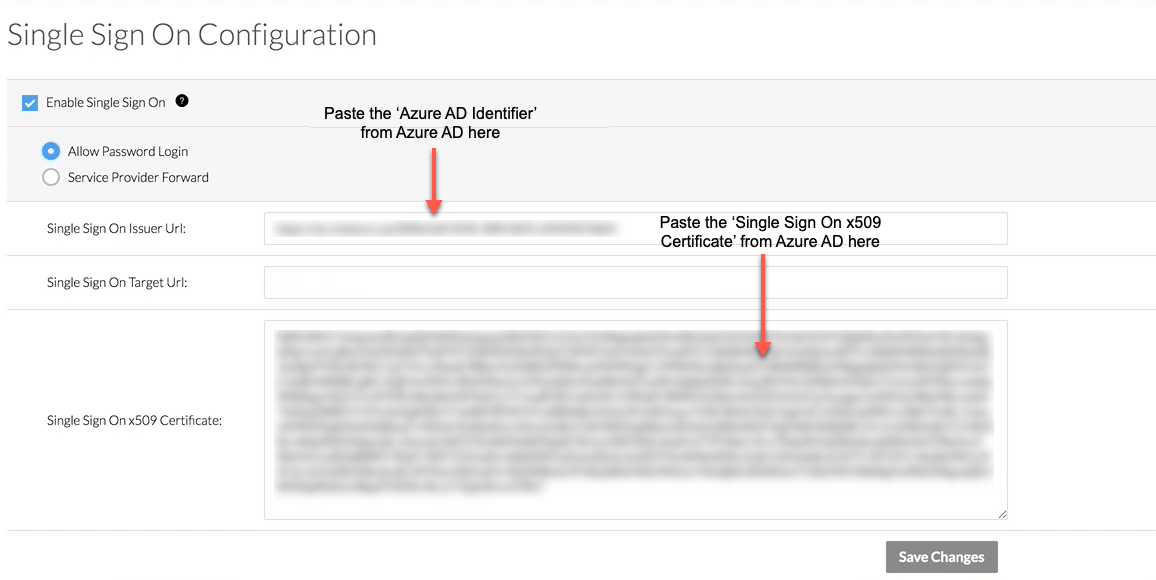
- Under Company Settings, click Single Sign On Configuration.
- Enter the following information:
- Allow Password Login
Choose this option to enable IdP-initiated SSO. - Single Sign On Issuer URL (Required)
Paste the 'Azure AD Identifier' that you obtained from Azure Active Directory in this field. - Single Sign On Target URL (Optional for IdP-Initiated SSO)
Paste the 'SAML Single Sign-On Service URL' into this field.
Note: Although this is an optional field for IdP-Initiated SSO, Procore recommends completing the data entry in this field now to make any future transition from IdP- to SP-initiated SSO smoother. - Single Sign On x509 Certificate (Required)
Paste the information from the certificate that you downloaded from Azure Active Directory.
Important! When copying the certificate information from , do NOT copy the "------------BEGIN CERTIFICATE------------" and "------------END CERTIFICATE------------" markers. You only want to copy the text that resides between these markers.
- Allow Password Login
- Scroll to the bottom of the page, and click Save Changes.
- Next, reach out to your company's Procore point of contact or contact Procore Support to request that they enter the domain(s) you want to target for authentication via SSO. Procore must enter these domains on your behalf.
- Once the domain(s) have been entered by Procore, take the final steps to enable SSO for your company:
- Mark the Enable Single Sign On box in Procore's SSO configuration settings.
- Select Allow Password Login to enable an IdP-initiated flow.
- Click Save.
Authentication via the configured SSO method will become active immediately after saving the final completed configuration.
PROCORE SUPPORT: INTERNAL NOTE
Perform the steps below when notified by the Procore Administrator that the SSO configuration is complete:
- When notified by the Procore Administrator that the SSO configuration is complete, please be sure that the following fields are filled out:
- Single Sign On Issuer URL
- Single Sign On Target URL
- Single Sign On x509 Certificate
- Once confirmed, the domain(s) will need to be filled out by any employee on the @sup_sso ping. Please reach out to the @sup_sso team in #dept-cs-core.
- Once done, the client will be able to check the box for 'Enable Single Sign On'. When they do, they will see the following two options: ' Allow Password Login' (refers to IdP-Initiated) and 'Service Provider Forward' (refers to SP-initiated). We typically recommend they try 'Allow Password Login' first to test the connection.